On February 21st 2025, approximately $1.46 billion in cryptoassets were stolen from Bybit, a Dubai-based exchange. Initial reports suggest that malware was used to trick the exchange into approving transactions that sent the funds to the thief.
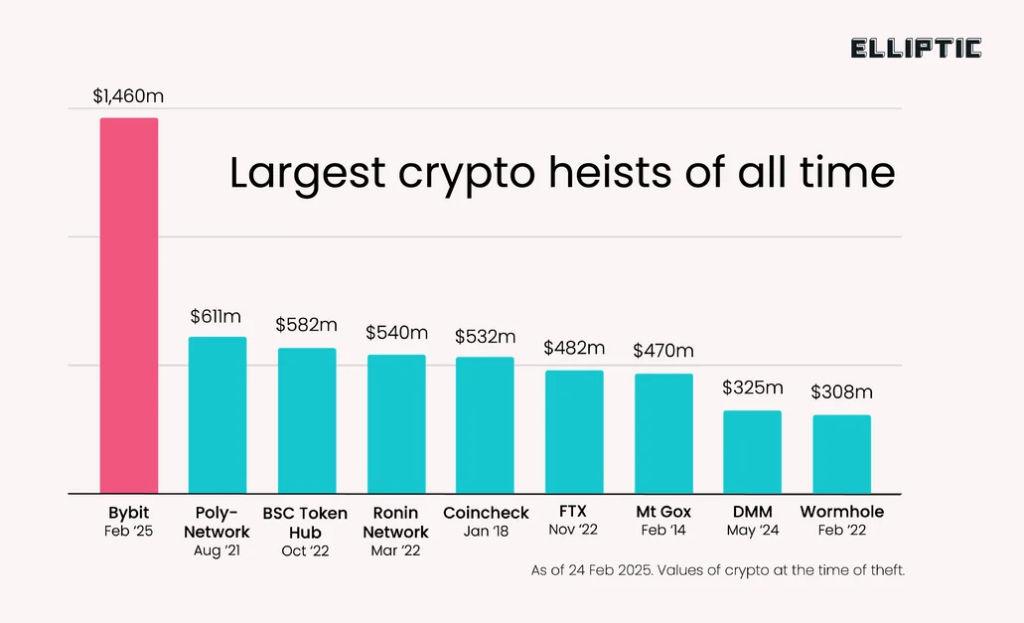
This is by the far the largest crypto heist of all time, dwarfing the $611 million stolen from Poly Network in 2021 (and the vast majority of these funds were eventually returned by the hacker). In fact this incident is almost certainly the single largest known theft of any kind in all time, a record previously held by Saddam Hussein, who stole $1 billion from the Iraqi Central Bank on the eve of the 2003 Iraq War.
North Korea’s laundering process typically follows a characteristic pattern. The first step is to exchange any stolen tokens for a “native” blockchain asset such as Ether. This is because tokens have issuers who in some cases can “freeze” wallets containing stolen assets, whereas there is no central party who can freeze Ether or Bitcoin.
This is exactly what happened in the minutes following the Bybit theft, with hundreds of millions of dollars in stolen tokens such as stETH and cmETH exchanged for Ether. Decentralised exchanges (DEXs) were used to achieve this, likely to avoid any asset freezing that might be encountered when using a centralised exchange to launder stolen funds.
The second step of the laundering process is to “layer” the stolen funds in order to attempt to conceal the transaction trail. The transparency of blockchains means that this transaction trail can be followed, but these layering tactics can complicate the tracing process, buying the launderers valuable time to cash-out the assets. This layering process can take many forms, including:
- Sending funds through large numbers of cryptocurrency wallets
- Moving funds to other blockchains, using cross-chain bridges or exchanges
- Switching between different cryptoassets, using DEXs, coinswap services or exchanges
- Using “mixers” such as Tornado Cash or Cryptomixer.
North Korea is currently engaged in this second stage of laundering. Within two hours of the theft, the stolen funds were sent to 50 different wallets, each holding approximately 10,000 ETH. These are now being systematically emptied – as of 8.30am UTC on February 27, 46% of the stolen assets (now worth $626 million) have been moved from these wallets.
