On February 21, 2025, Bybit, a prominent cryptocurrency exchange, experienced a significant security breach resulting in the loss of nearly $1.5 billion worth of ether (ETH). This incident stands as the largest digital heist in the history of cryptocurrency. Fortunately, Bybit is actively collaborating with industry experts, including Chainalysis, to trace the stolen assets. They have also launched a recovery bounty program, offering up to 10% of the recovered amount to individuals who assist in retrieving the stolen crypto.
Below is a step-by-step analysis of how the Bybit exploit unfolded:
- The compromise: The hackers gained access to a Safe developer’s computer to control the Safe UI that was specifically used for Bybit transactions. They then added the malicious JavaScript snipped to the frontend code, to make it appear that Bybit was signing a legitimate transaction, when in fact it was a malicious one.
- Initiation of unauthorized transfers: During what appeared to be a routine transfer from Bybit’s Ethereum cold wallet to a hot wallet, Bybit unknowingly signed the malicious transaction, enabling the attackers to move approximately 401,000 ETH — valued at nearly $1.5 billion at the time of the exploit — to addresses under their control.
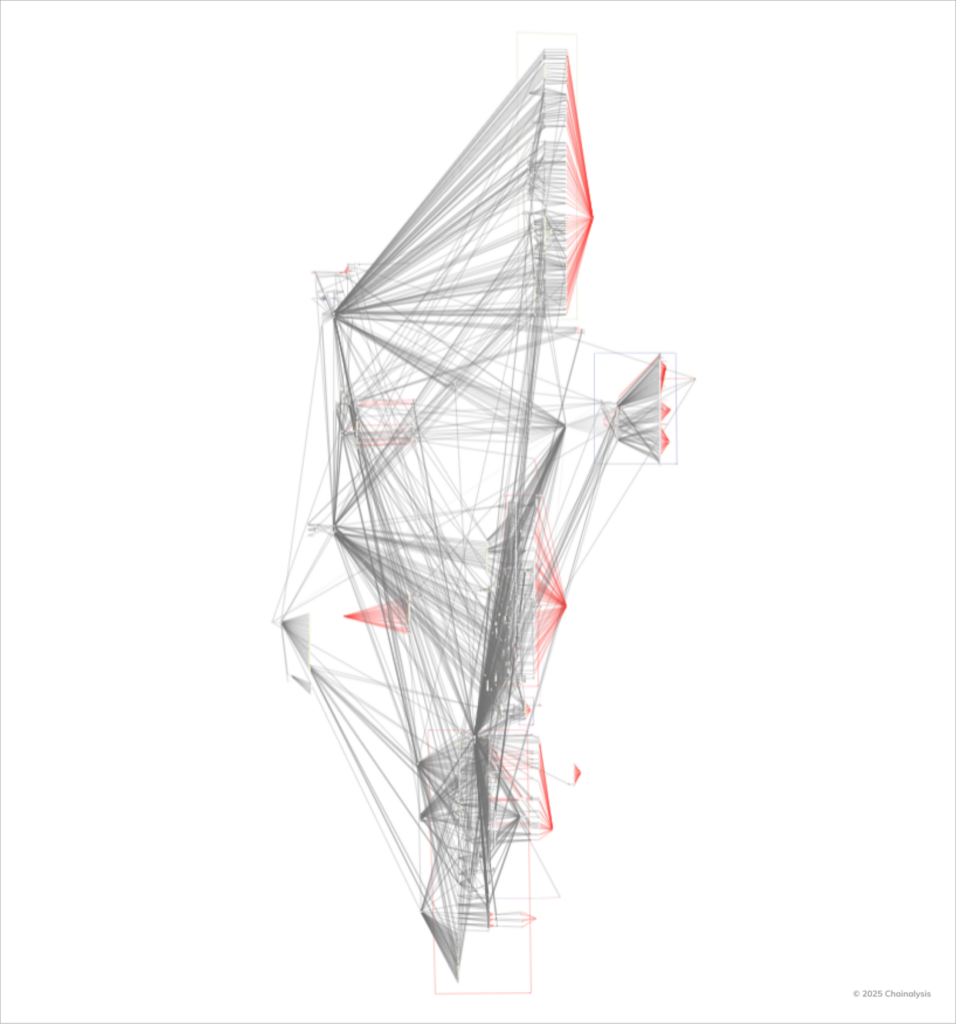
- Asset dispersion through intermediary wallets: The stolen assets were then moved through a complex web of intermediary addresses. This dispersion is a common tactic used to obfuscate the trail and hinder tracking efforts by blockchain analysts.
- Conversion and laundering: The hackers swapped significant portions of the stolen ETH for tokens including BTC and DAI. They also utilized decentralized exchanges (DEXs), cross-chain bridges, and a no-KYC instant swap service to move assets across networks.
- Keeping funds dormant and strategic laundering: A notable portion of the stolen funds has remained idle across various addresses, a deliberate move often employed by North Korea-affiliated hackers. By delaying laundering efforts, they aim to outlast the heightened scrutiny that typically immediately follows such high-profile breaches.
Despite the severity of Bybit’s attack, the inherent transparency of blockchain technology presents a significant challenge for malicious actors attempting to launder stolen funds. Every transaction is recorded on a public ledger, enabling authorities and cybersecurity firms to trace and monitor illicit activities in real time.
Collaboration across the crypto ecosystem is paramount in combating these threats. The swift response from Bybit, including its assurance to cover customer losses and its engagement with blockchain forensic experts, exemplifies the industry’s commitment to mutual support and resilience. By uniting resources and intelligence, the crypto community can strengthen its defenses against such sophisticated cyber attacks and work toward a more secure digital financial environment.
https://www.chainalysis.com/blog/bybit-exchange-hack-february-2025-crypto-security-dprk/
